Stop Social Engineering Attacks is one of the most important ways toprotect your digital or real life from any attempt to steal, hack, or seizeit.
Such digital charades are designed not to sneak in with a line of code, butused to prey on human vulnerabilities in terms of emotion, lack ofexperience, education, or proper guidance.
Because of the seriousness of this type of attack, in this article we willdelve into the complex world of social engineering attacks, and discoverwhat types of social engineering attacks are, in addition to ways toprotect and detect them.
What are Social Engineering Attacks
Many online thefts and hacks are caused by social engineering, which isstrategies cybercriminals use to exploit human psychology and behavior inorder to deceive, gain unauthorized access to, or manipulate victims intoperforming actions that threaten their security and the security of their sensitive data.
Instead of attacking technical vulnerabilities directly, this type of attackrelies on tricking people into accessing information, clicking on links, ortaking an action that gives the attacker unauthorized access.
Types of social Engineering Attacks leverages various psychological factorsof human, including trust, authority, fear, curiosity, and helpfulness.
Social engineering attacks can take many forms to reach their target,lick phishing emails, or phone calls from individuals posing astechnical support.
What are Types of social Engineering Attacks?
Hacking through social engineering is not just a name, but under this namecome many Types of social Engineering Attacks under him.
You will be truly surprised by the methods used by fraudsters, as they usesocial engineering methods to reach their goals, including:
- Phishing: Attackers send scam emails or messages that appear to be from legitimate sources (such as banks, social media platforms, colleagues, or real companies), with the aim of tricking recipients into revealing personal information, credentials, or financial details.
- Targeted Phishing: Similar to phishing, but more targeted, the attacker tailors messages in a more professional way to a specific individual or organization, often using personal information to increase the likelihood of success.
- Whaling: A form of phishing that targets very important individuals, such as CEOs of companies or organizations, to gain access to valuable information or resources.
- Phishing (voice phishing): Phone calls impersonating legitimate organizations, often pretending to be customer service representatives, are used to manipulate victims into revealing sensitive information.
- Pretext: Attackers create a fabricated scenario or pretext to manipulate individuals into providing information or performing actions they would not normally do.
- Software phishing: Attackers offer something enticing, such as a free software download or physical item, to lure victims into performing an action that compromises their security.
- Quid Pro Quo: Attackers promise a benefit or service in exchange for sensitive information, often under the pretext of technical support.
- Tracking(s): Attackers physically track authorized employees to secure areas by posing as employees or contractors.
- Impersonation: Attackers impersonate a trusted person, such as a co-worker, to manipulate victims into sharing information or performing actions.
- Dumpster diving: Attackers examine discarded physical documents, such as papers in trash cans, to find valuable information.
- Reverse social engineering: Attackers manipulate victims into asking for help or advice, allowing the attackers to gain access to sensitive information or systems.
- Honey trap (Honeypot): Attackers create a fake persona or online presence to build a relationship with victims and extract information from them.
- Quizzes, surveys, and contests: Attackers create fake quizzes, surveys, or contests that ask for personal information as part of the sign-up process.
- Online Impersonation: Attackers create fake social media profiles or websites to impersonate someone and gain the trust of potential victims.
- Watering Hole Attack: Attackers compromise websites frequented by a specific group of users and insert malicious code to infect visitors’ devices.
Here are some warning signs to watch out for:
- Urgency/Pressure: Pressured for quick action.
- Sensitive Info: Asked for personal/confidential data.
- Unknown Source: Communication from unfamiliar sender.
- Offers that are too good to be true: Unrealistic offers or prizes.
- Emotional Manipulation: Playing on emotions to comply.
- Unauthorized Access: Request for unapproved access.
- Inconsistent Comm: Errors, mistakes, inconsistencies.
- Impersonation: Pretending to be someone trusted.
- Odd Friend/Coworker Requests: Unusual money or info asks.
- Unsolicited Attachments/Links: Beware of unknown links.
- Suspicious URLs: Check before clicking.
- Money/Gift Card Requests: Urgent money needs.
- Employee Behavior Changes: Unusual requests/actions.
- Manipulation of Authority: Fake higher-ups or jargon use.
What is The Most Effective way to detect and stop Social EngineeringAttacks?
These attacks pose a major threat to individuals and organizations alike.
To effectively address them, we need a multipronged approach that includesmaking security an ingrained part of our company culture.
Let’s explore some basic strategies for detecting and stopping socialengineering attacks.
Make security part of your company’s culture
The best possible attack is defense.
Strong awareness and taking responsibility are one of the most importantways to protect yourself or your business from any potential threat, whetherit is hacking through social engineering, or through malicious software suchas viruses.
Educate your employees
Continuous education and training courses for employees through trainingprograms on the dangers of social engineering and ways to deal with them mayprevent any institution or individual from falling into the trap of socialengineering.
Employees are the first line of defense against any potential attack, and byknowing and detecting the warning signs of social engineering attacks, thesecurity level can be maintained at its maximum.
Use two-factor or multifactor authentication
Implementing strong authentication methods is an important step in thwartingsocial engineering attacks.
Two-factor authentication (2FA) or multifactor authentication (MFA) adds anextra layer of security beyond just entering passwords.
Even if an attacker gains access to your registration data, they will stillneed a secondary verification step, such as a text message or biometricscan, and this greatly reduces the risk of unauthorized access.
Implementation of cybersecurity tools and protection programs
Leveraging advanced cybersecurity tools can significantly enhance yourdefense against social engineering attacks.
Intrusion detection systems, email filters , endpoint protection software, and antivirus software are among the manytools that can help identify and block malicious activity.
These tools can analyze patterns, behaviors, and content to detect potentialthreats in real-time, providing an additional layer of protection.
Data backup
In the event of a successful malware attack or social engineering hack,backing up data before the breach occurs can be a lifesaver.
Ransomware attacks, often facilitated by social engineering, can lead todata encryption and payment demands.
If you have secure backups, you can restore your systems without giving into the attacker’s demands.
Conclusion
Social engineering hacking methods are a testament to the ingenuity ofcybercriminals in reaching their targets.
By exploiting human psychology and poor training and education, theseattacks remind us that the human factor remains the weakest link in thesecurity chain.
Staying informed, cultivating skepticism, and investing in technology areour arsenal against the web of phishing and any method of hacking.
The battle against social engineering tactics is an ongoing battle, and itis a battle where knowledge and vigilance are the most powerful weaponspossible.

The 7 Best Antivirus with AI To Protect You From Security Threats
By Zouani in - 16 Mar, 2024
Kaspersky Vs Windows Defender: Which Is Better For Security
By Zouani in - 16 Feb, 2024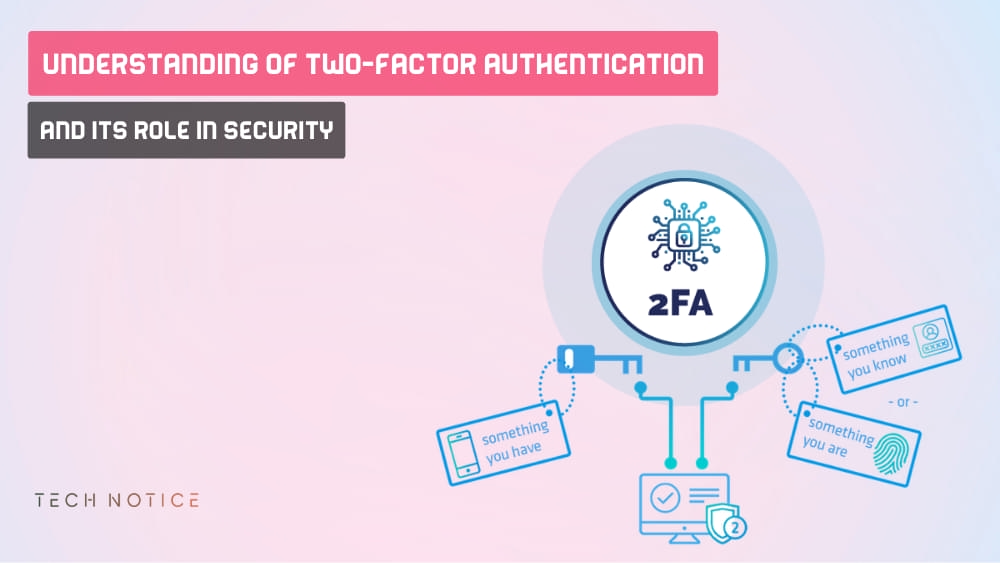
Understanding Of Two-Factor Authentication (2FA) And Its Role In Security
By Zouani in - 17 Jan, 2024
Difference Between Bitdefender Vs Kaspersky Antivirus: Which Is Best?
By Zouani in - 17 Jan, 2024
Ultimate Guide To Downloading From Torrenting Safely In 2025
By Zouani in - 18 Dec, 2023
6 Best Most Secure Web Browsers In 2025: (Which Is Best For You?)
By Zouani in - 18 Nov, 2023